Automate Patch Management
Action1 enables you to automate the patch management process and tailor it to your corporate update policy. Automated operations, or automations, allow you to roll out updates and patches in a time slot that is the most convenient for both system administrators and remote users. Implementing automated patch deployment strengthens overall security and ensures critical updates will not be overlooked.
An automation comprises:
- Action that defines what to do – run script, deploy updates, etc.
- Scope that defines where to run – endpoints or groups.
- Schedule that defines when to run – once or regularly on the specified day/time.
NOTE: To create an automation, a user role with at least Manage Automations permission is required.
To create an automation for update deployment:
- Navigate to the Automations page
- Select New Automation | Deploy Update to start the wizard.
TIP: To roll out updates in stages, you can use a new Update Ring automation. See Update Rings for details.
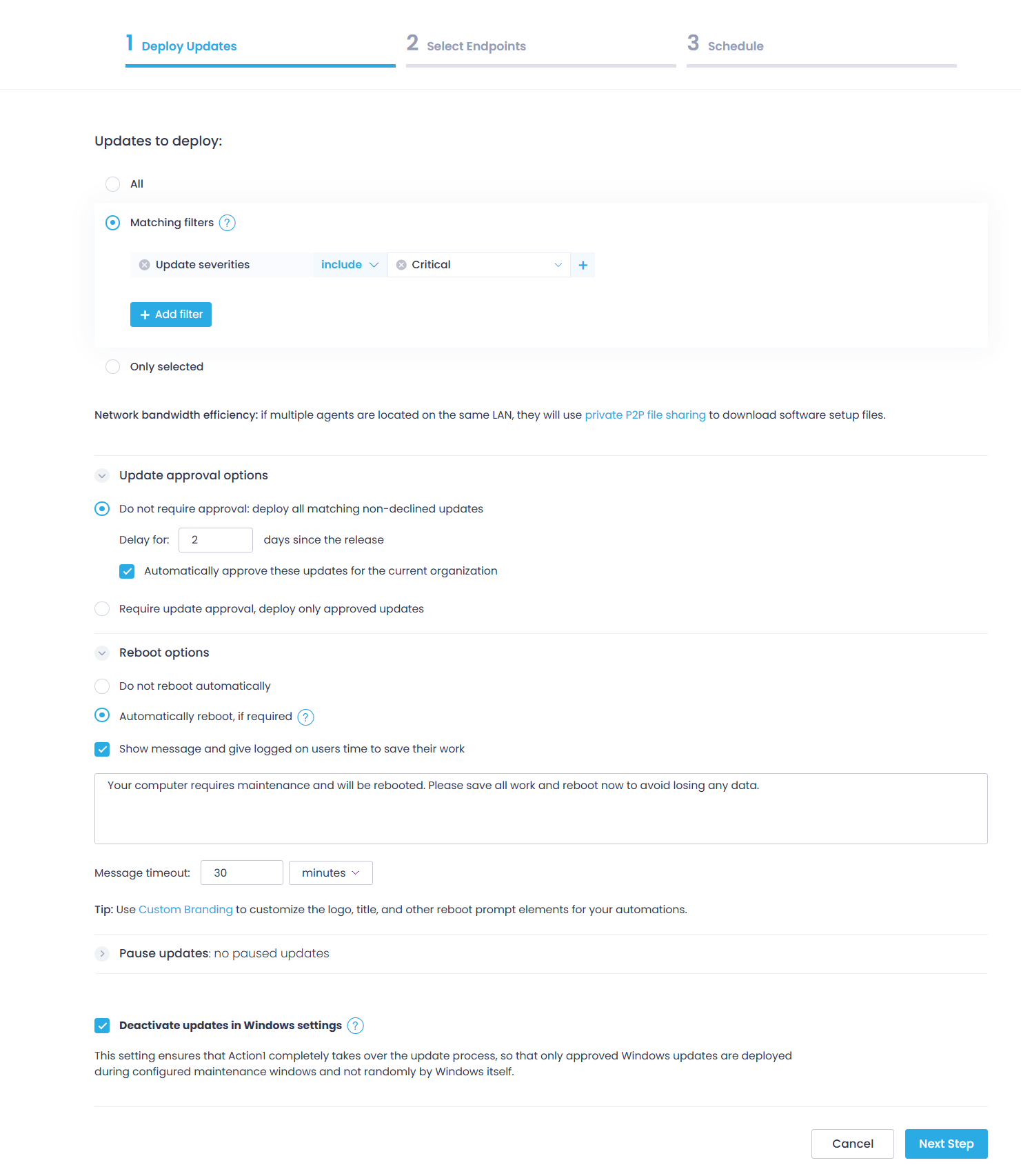
Step 1: Deploy Update
On this step, do the following:
- Select the updates for deployment on the managed endpoints.
- All — use this option to install all updates, irrespective of their severity or status.
- Matching filters — use this option to install the updates that match your search criteria. Add filters such as update source, update severity, etc.
- You can add several filters, and Action1 will search for and deploy updates that match them all at once (logical AND).
- Within each filter, you can provide several values, and Action1 will search for any of them (logical OR).
- The values can be included or excluded. For example, search for and deploy security updates that are coming from Microsoft or Google, but which severities are anything except Low.
- Only selected — use this option to install specific updates you’ve picked.
- Configure update approval options: specify whether you need updates to be explicitly approved before they can be scheduled for distribution. By default, the first option Do not require approval: deploy all matching non-declined updates will be applied.
- Set the time to wait before automatically installing an update (in days after the release).
Important! Due to the existing product peculiarities, for the DEB Linux packages, you should enter 0 in this field. Otherwise, updates of DEB packages will not be automatically deployed. For RPM packages, this option works normally.
-
- If you want to automatically approve these updates for the current organization, select the corresponding option.
NOTE: To use the Auto-approve updates option, the Approve Updates permission will be required.
-
- Alternatively, if you plan to approve the updates manually before deployment, select Require update approval, deploy only approved updates. For details on the approval process, refer to Review and Approve Update.
- Next, specify the required Reboot options — to skip or allow rebooting required for the update. You can configure the reboot timeout and notification for a user whose computer is going to be restarted. To learn more about these settings, refer to Updates Deployment and Reboot Behavior on Windows and Updates Deployment and Reboot Behavior on macOS.
- If you need to exclude the selected software update from deployment, add it to the Pause updates list. See also: Software Updates: View Deployment Status & Pause Deployment.
- (Windows Updates only) If you want to disable Windows Update and distribute patches and KBs via Action1 only, select Deactivate updates in Windows settings.
NOTE: If automatic updates are already configured using Group Automation (GPO), this setting will not take effect.
How this setting works
When enabled, this setting runs the built-in script Deactivate Updates in Windows Settings on the target endpoint(s), which modifies Windows Update registry settings in HKLM\SOFTWARE\Policies\Microsoft\Windows\WindowsUpdate\AU.
The script sets the registry value NoAutoUpdate=1
- This disables automatic Windows updates, allowing Action1 to fully control update deployment.
- However, if automatic updates are already configured using Group Policy, the setting remains unchanged.
Additionally, Action1’s real-time missing update detection mechanism (which runs every few minutes) enables monthly Windows cumulative updates (known as “Patch Tuesday”) on systems not running the latest Windows version. This is accomplished by pausing the preview and feature updates and effectively disabling uncontrolled Windows upgrades. Registry settings affected: DeferFeatureUpdates, DeferFeatureUpdatesPeriodInDays, and PauseFeatureUpdatesStartTime.
Note: These registry settings persist after the agent is removed. To restore the default Windows Update behavior, run the built-in script Activate Updates in Windows Settings before uninstalling the agent.
Step 2: Select Endpoints
On this step, pick the applicable managed endpoints. You can add endpoints one by one, select a group, or select all.
Consider the following:
- Creating an automation for a group of endpoints is only allowed if all endpoints in the group are visible (that is, are within the scope of the user’s View Endpoints permission). Visibility may be limited if the group contains endpoints that belong to another group excluded by the View Endpoints permission.
- Similarly, specifying individual endpoints by ID is restricted if those endpoints are part of a group that has been excluded through the View Endpoints permission.
- To specify ALL as target endpoints for the automations, the View Endpoints with Organization scope will be required.
To learn more about permissions, see Permissions in Detail.
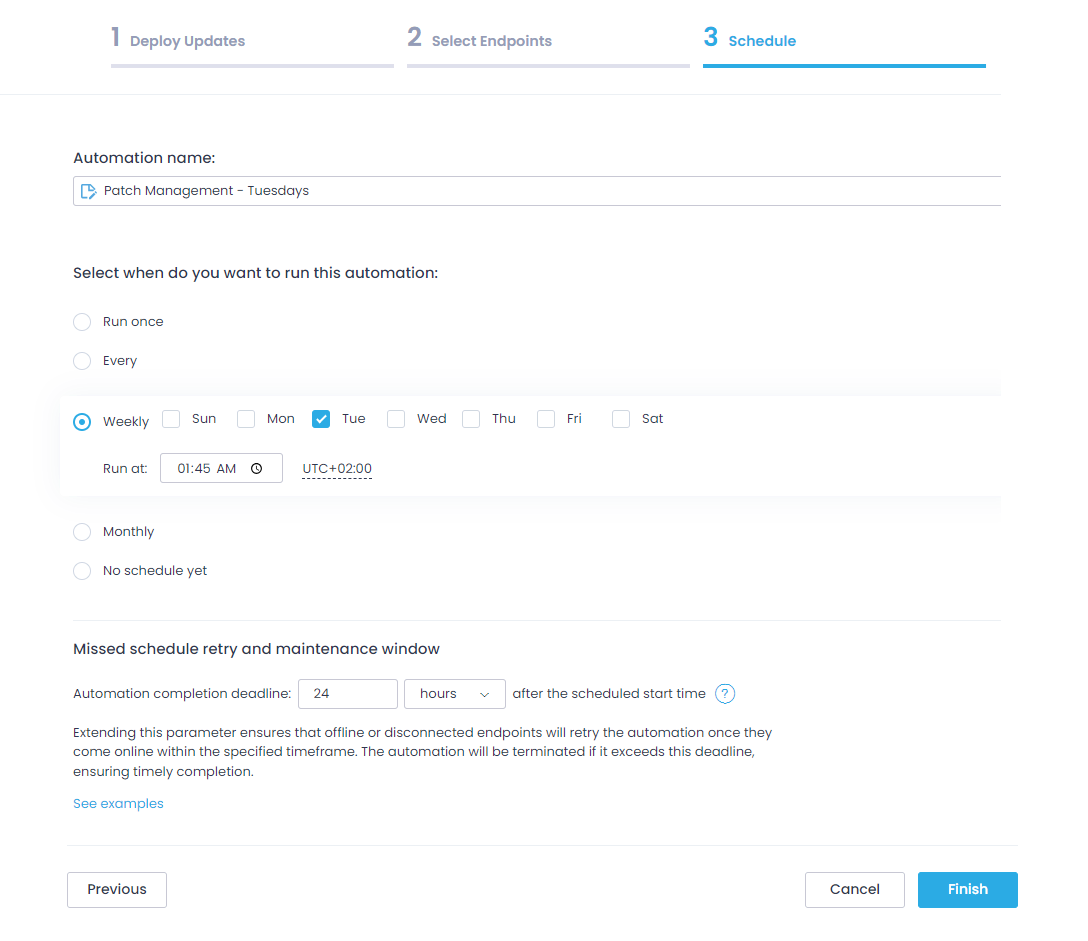
Step 3: Schedule
On this step, do the following:
- Enter a name for the new automation (e.g., “Windows Patch Management”).
- Configure the patching schedule. Set the time that works best for your team, for example, Tuesday morning.
- Specify Missed schedule retry and maintenance window – a timeframe to retry update delivery for the powered-off or disconnected endpoints.
Important! The automation will be terminated if it exceeds this deadline. Also, make sure this window does not exceed the frequency of execution, i.e., do not set it to 3 days for automations running on a daily basis.
Alternatively, you can configure the automation to Run once (after you finish the wizard, or at the specified time).
- Click Finish.
See also: Managing Automations