Endpoint Security & Configuration
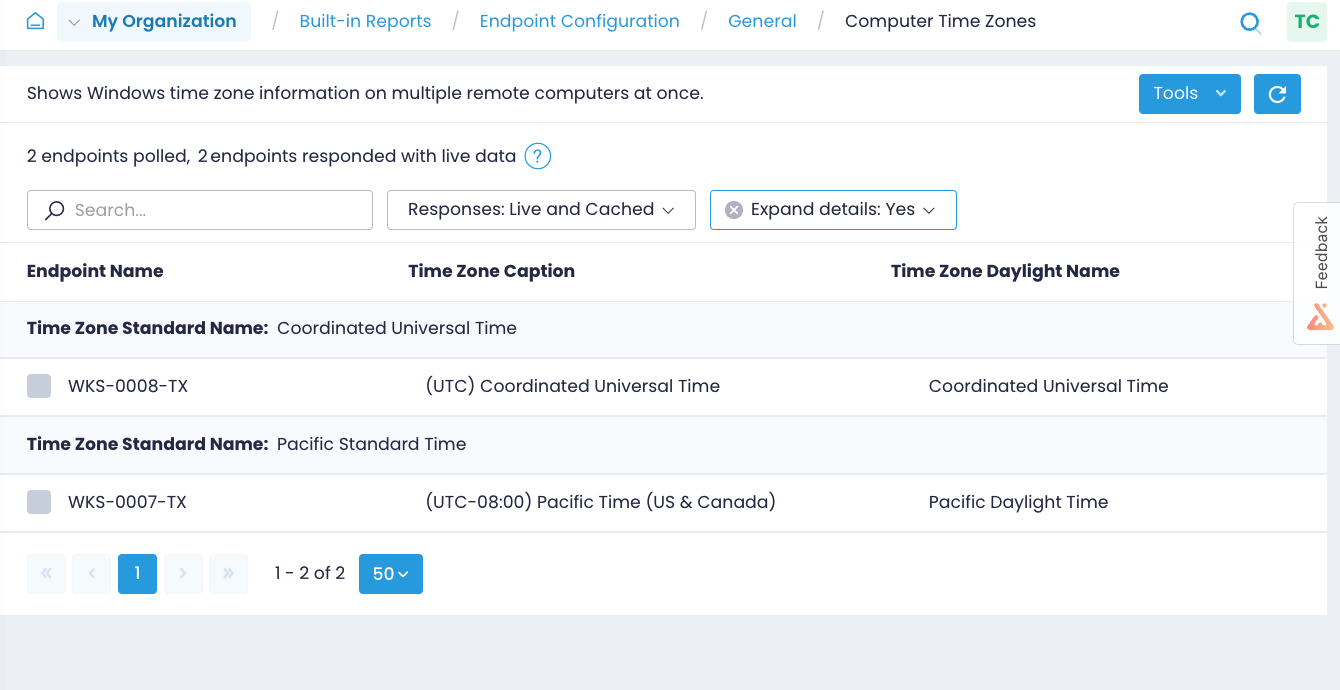
Action1 provides unique endpoint management tools and enables you to get real-time security information from your entire network of endpoints. Dozens of reports are provided out of the box, addressing the most common security and operational needs. To browse reports, navigate to Real-Time Reports & Alerts / Built-in Reports / Endpoint Security or Endpoint Configuration. For your convenience, Action1 provides reports that cover most configuration and security aspects such as network topology, users and groups, shared folders, boot configurations, time zones, environment variables, and many more. With Action1 reports, you can explore endpoint configuration and assess your endpoint health state.
Switch between live and cached data and drill down to details. Use Tools to see additional actions. Each report you can export as CSV or HTML. To receive a report on a regular basis, select Subscribe or choose Create Alert to receive instant notifications on changes. If interested in customizing a report, Clone it first.