Any newly installed software on your company’s workstations can be the first alert indicating a data breaches at a very early stage. Monitoring all Teamviewer endpoints and proactively blocking all unauthorized installations it is a critical procedure that shall be performed by all departments on an ongoing basis.
TeamViewer — freeware software designed for remote administration, transferring files between multiple systems (including mobile), conducting presentations and visual training with a demonstration of the desktop, applications and individual files: due to the support of an enormous number of operating systems, a peep possible in every corner of the world without any settings!
Extremely popular, convenient and useful tool for organizing remote access was appreciated not only by system administrators and developers, but also by everyone who at least once had to urgently connect to a work computer during a business trip, vacation or from home. However, the uncontrolled use of such software poses a threat to the security of the company and may lead to incidents.
From the point of view of information security, Teamviewer endpoints are a threat to the perimeter violation of the corporate network — both in the case of Teamviewer uncontrolled use, and in the case of neglect of security rules when connecting to the corporate network from outside. At the same time, the activity of such software on the network significantly complicates the identification of malicious activity against a legal background. In addition, if there is no agreement on the use of remote access software with the IT security service, its detection on the network may indicate successful intruders.
To reduce the risk of such incidents, you should force security measures and limit the use of software for remote access as much as possible — for example, using application controls. In the case when the use of such software by employees is part of business processes, it is necessary to limit the potential of the potential attacker as much as possible. Thus, the use of HIPS policies, launch with minimal privileges, mandatory domain and, at best, two-factor authentication, will help reduce the risks of using potentially dangerous software to an acceptable level.
Below there are a ways to get a list of installed software and monitoring all teamviewer endpoints to prevent data breaches and avoid unauthorized access.
Manually:
Option 1: Via Control Panel on a Local Computer:
1. Open Windows Explorer (Win+E)
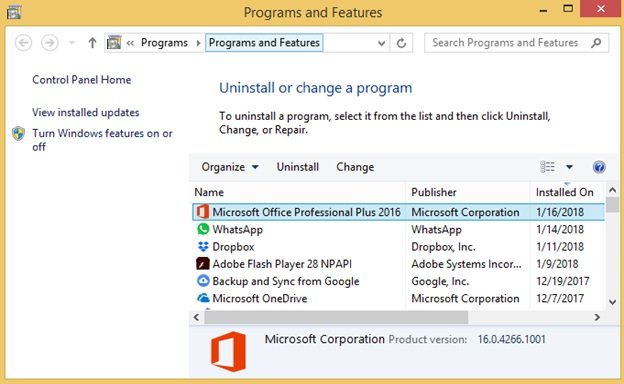
2. Navigate to ‘Control Panel\Programs\Programs and Features’ to display the following screen:
3. Click on ‘Installed On’ column to sort by installed date and have the most recently installed programs pop up on top.
Option 2: Via Wmic Utility on a Remote Computer:
1. Launch PowerShell command prompt (press Win+R, type ‘powershell’, Enter)
2. In the PS command prompt, Get-WmiObject -Class Win32_Product -Computer computername | Select-Object Name,InstallDate | Sort-Object InstallDate
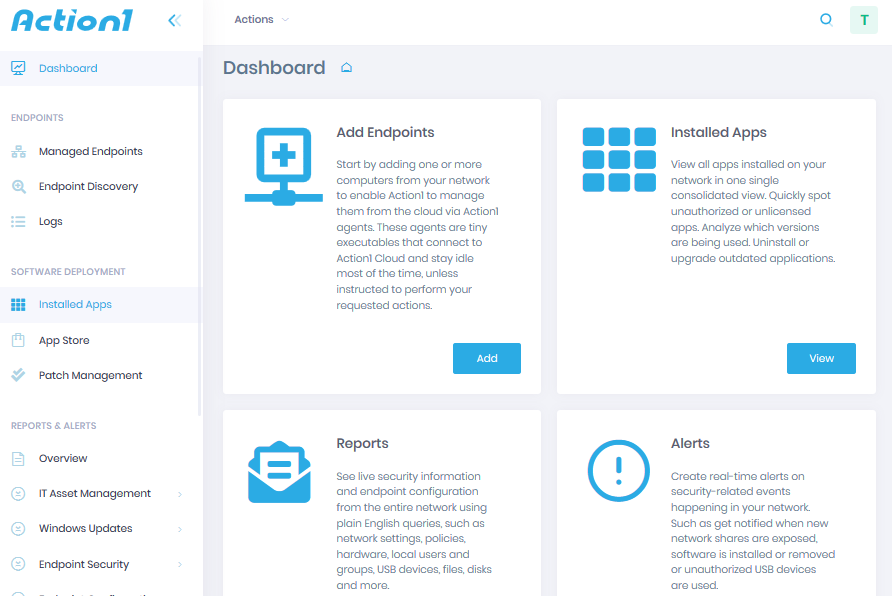
With Action1:
Step 1 — Sign-up for Free:
Action1 is a cloud-based platform for automated patch management, software asset management, remote desktop, and unattended access.