Any newly installed software on your company’s workstations can be the first alert indicating a data breaches at a very early stage. Monitoring all software installation events and proactively blocking all unauthorized installations it is a critical procedure that shall be performed by all departments on an ongoing basis.
Join.me.exe is a type of EXE file associated with Join.Me developed by Logmein, Inc. for Windows. The latest known version of Join.me.exe is 1.9.1.204, which was produced for Windows. This EXE file has a popularity rating of 1 stars and a security rating of ‘UNKNOWN’.
EXE (‘executable’) files, such as join.me.exe, are files that contain step-by-step instructions that a computer follows to carry out a function. When you double-click an EXE file, your computer automatically executes these instructions created by the program developer (for example, Logmein, Inc.) to launch a program (for example, Join.Me) on your computer.
Each software application on your computer uses an executable file: your web browser, word processor, spreadsheet program, etc. This makes executable files one of the most useful kinds of files in the Windows operating system. Without executable files like join.me.exe, you could not use any programs on your computer.
Below there are a ways to get a list of installed software and monitoring all software installation to prevent data breaches and avoid unauthorized access.
Manually:
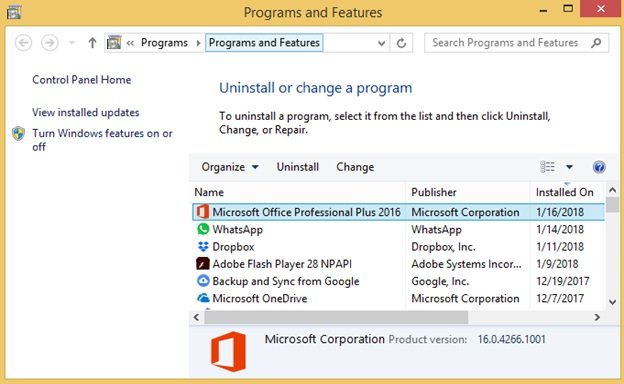
Option 1: Via Control Panel on a Local Computer:
1. Open Windows Explorer (Win+E)
2. Navigate to ‘Control Panel\Programs\Programs and Features’ to display the following screen:
3. Click on ‘Installed On’ column to sort by installed date and have the most recently installed programs pop up on top.
Option 2: Via Wmic Utility on a Remote Computer:
1. Launch PowerShell command prompt (press Win+R, type ‘powershell’, Enter)
2. In the PS command prompt, Get-WmiObject -Class Win32_Product -Computer computername | Select-Object Name,InstallDate | Sort-Object InstallDate
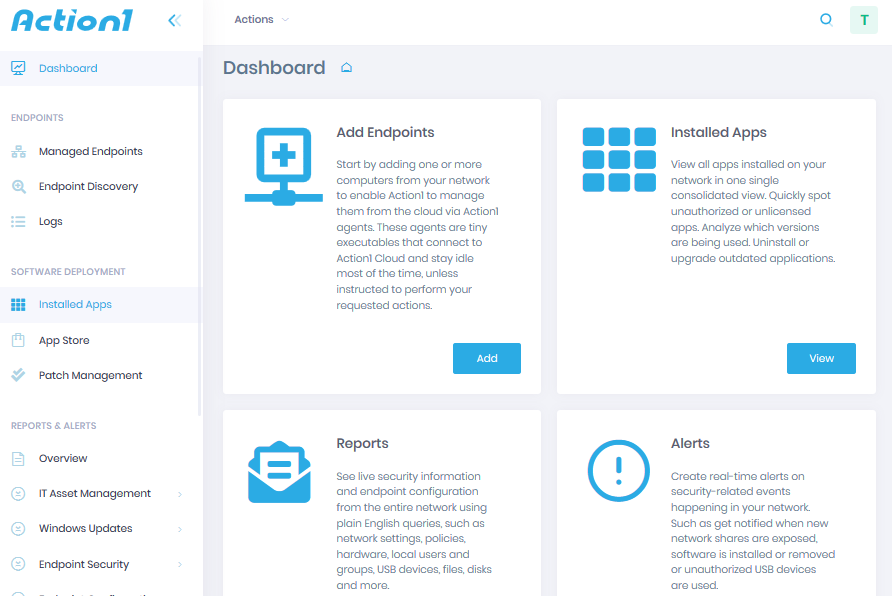
With Action1 Endpoint Security Platform:
Step 1 — Sign-up for Free:
Sign up for a free version of the Action1 solution and install Action1 agents to your remote endpoints to manage them remotely. Here is the detailed instruction on how to get started.
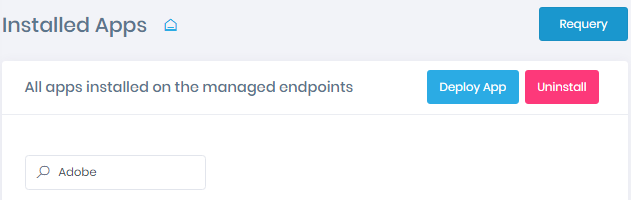
Step 2 — Type Your Question in Plain English
Step 3 — Set Filters, If Necessary: