Remote access tool are a good way to save time for remote administration and other related tasks. It is well known that such programs are not always used for good. Malefactors apply similar means or their specialized analogs for achievement of the mercenary purposes.
Below there are a ways to get a list of installed software and VNC tracking to avoid unauthorized access.
Manually:
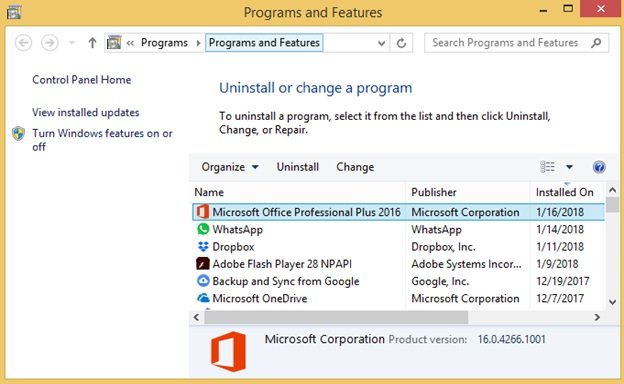
Option 1: Via Control Panel on a Local Computer:
1. Open Windows Explorer (Win+E)
2. Navigate to ‘Control Panel\Programs\Programs and Features’ to display the following screen:
3. Click on ‘Installed On’ column to sort by installed date and have the most recently installed programs pop up on top.
Option 2: Via Wmic Utility on a Remote Computer:
1. Launch PowerShell command prompt (press Win+R, type ‘powershell’, Enter)
2. In the PS command prompt, Get-WmiObject -Class Win32_Product �Computer computername | Select-Object Name,InstallDate | Sort-Object InstallDate